Framework mapping
Translate overlapping requirements into one shared control model instead of maintaining duplicate work for every framework.
Cocoon CS gives regulated organizations one place to manage cybersecurity compliance across CMMC, CP-CSC, ISO 27001, SOC 2, EU CRA, NIS2, and related buyer requirements.
Replace disconnected spreadsheets, point tools, and one-off consulting workflows with a governed operating model for controls, evidence, supplier posture, and executive visibility.

Translate overlapping requirements into one shared control model instead of maintaining duplicate work for every framework.
Collect, review, reuse, and govern evidence so audit preparation becomes a continuous process instead of a scramble.
Bring controls, policies, risks, evidence, supplier reviews, and leadership reporting into a single execution environment.


Track supplier cybersecurity readiness, open issues, and evidence expectations as part of the same compliance program.
Give leadership a clear view of readiness, remediation momentum, and concentration of risk before buyers or regulators ask.
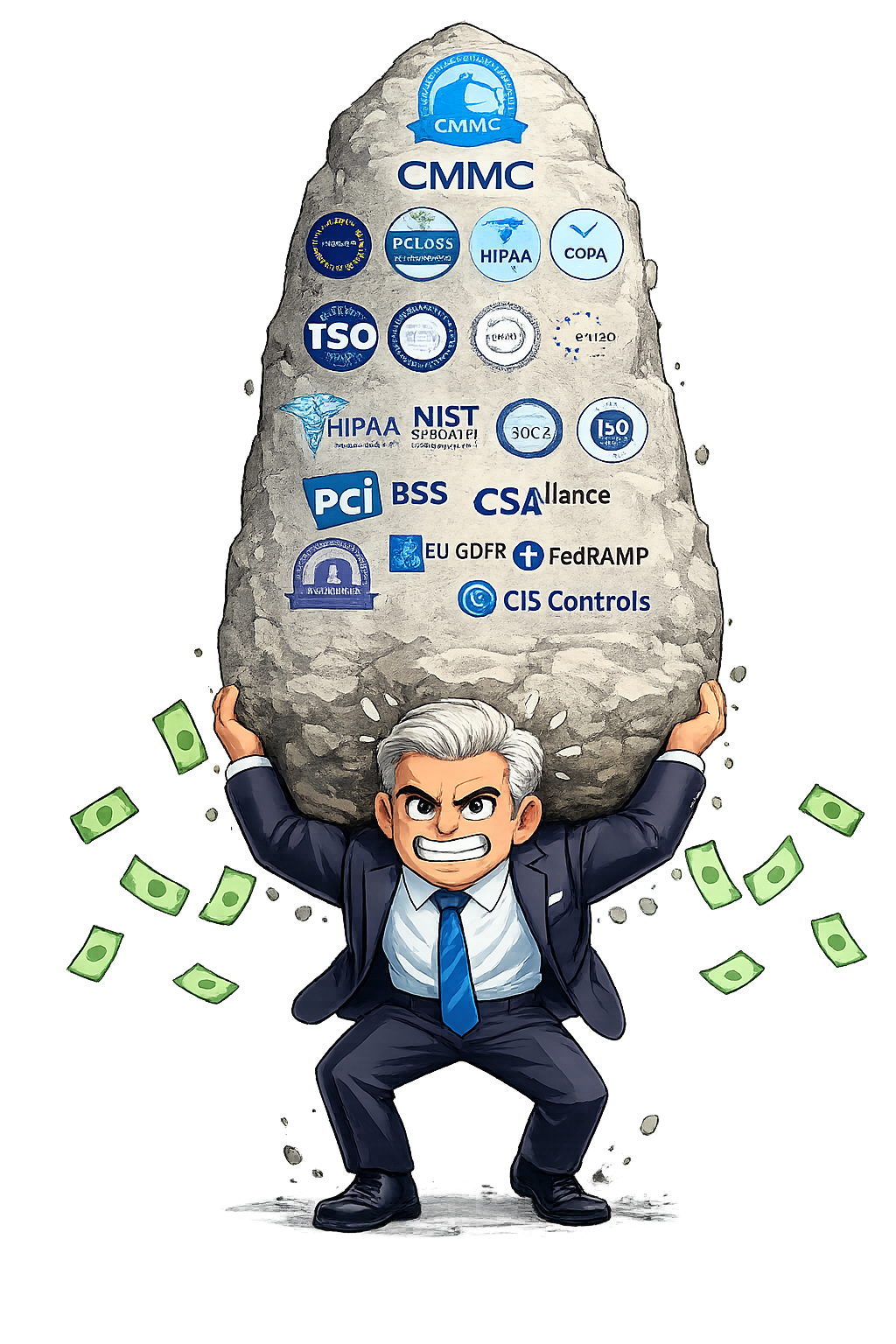
Cocoon CS helps organizations align 42+ security, privacy, and supply chain frameworks, including CMMC, CP-CSC, ISO 27001, SOC 2, EU CRA, and NIS2, through a single operational model for controls, ownership, and evidence.
That means less duplicated remediation, clearer accountability across teams, and a stronger path from program design to buyer-ready execution.

Cocoon CS combines platform workflows with expert-guided governance services so compliance teams can move from planning into measurable execution.
See where controls satisfy multiple obligations and reduce duplicate work across defense, enterprise, and regulatory demands.
Keep critical evidence, remediation records, and risk decisions organized so audits, reviews, and renewals are easier to support.
Use Cocoon CS governance services to accelerate setup, guide remediation planning, and maintain momentum across internal teams and suppliers.

Cocoon CS is designed to help teams start quickly, structure accountability, and keep evidence and remediation moving over time.
Map your current regulatory scope, buyer expectations, evidence gaps, and organizational constraints before building the working plan.
Organize controls, policies, risks, suppliers, and evidence into one operating model that internal teams can actually maintain.
Reuse evidence, track remediation to closure, and extend the same program into new frameworks, supplier reviews, and executive reporting needs.

Unify defense, enterprise, and regulatory requirements in one control model instead of rebuilding the program every time a new buyer or framework appears.

Replace evidence chasing with a repeatable workflow for collection, review, remediation, and audit support so readiness is maintained continuously.

Give leadership one source of truth for posture, supplier exposure, overdue work, and readiness momentum before a customer, auditor, or regulator asks.
Yes. Cocoon CS is designed to map overlapping requirements into a shared operational model so teams can manage several frameworks without duplicating the whole program.
No. Defense supplier requirements are a strong use case, but Cocoon CS also supports enterprise buyer programs and broader regulatory readiness across product, operational, and supplier obligations.
That is the goal. Cocoon CS centralizes controls, evidence, remediation, and reporting so teams do not have to stitch together manual files and disconnected tools.
Yes. Cocoon CS helps organizations bring supplier readiness, requested evidence, follow-up actions, and overall third-party cyber posture into the same governance workflow.
Most teams begin with a consultation to clarify obligations, current-state maturity, immediate buyer or regulatory pressures, and the fastest path to a governed execution model.
Yes. Cocoon CS is built to help teams extend an existing compliance operating model into additional regulatory demands instead of creating a brand-new program for each one.